Equipment Asa 5500 Performance
Engineered with precision and durability, the Asa 5500 offers unmatched reliability and efficiency in industrial applications. Discover innovative solutions with optimized performance for your business needs.
Talk to an expert
6 Matching results
ASA5520-MEM-2GB= (2GB MEMORY FOR CISCO ASA 5520)
4.6 (5)- N/A
- N/A
- N/A
- N/A
- N/A
- Computer Memory
- DDR4
Est Value$745.59
$104.38
86% offFirst-Time Buyer Discount – Get up to 2% additional off on your first order
ORM Rewards Earn $50 in Rewards + Free Expedited Delivery – Join Now!
Use eCoupon ORMSAVE10
eCoupon limited to 5 units
ASA5540-MEM-2GB= (2GB MEMORY FOR CISCO ASA 5540)
4.8 (5)- 0.08 lbs
- N/A
- Computer Memory
- DDR4
- Workstation
- UDIMM
- Standard
Est Value$657.57
$144.67
78% offFirst-Time Buyer Discount – Get up to 2% additional off on your first order
ORM Rewards Earn $50 in Rewards + Free Expedited Delivery – Join Now!
Use eCoupon ORMSAVE10
eCoupon limited to 5 units
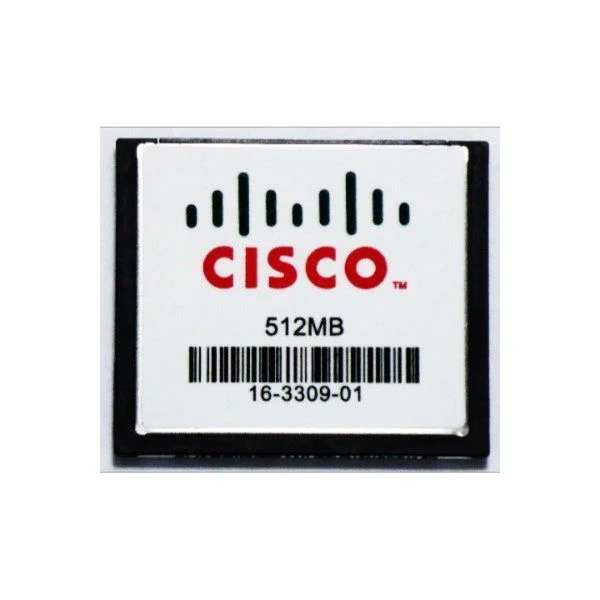
ASA5500-CF-512MB= (ASA 5500 SERIES COMPACT FLASH 512MB)
4.6 (5)- N/A
- N/A
- N/A
- N/A
- N/A
- Computer Memory
- Desktop / Laptop / Server
Est Value$581.70
$11.64
98% offFirst-Time Buyer Discount – Get up to 2% additional off on your first order
ORM Rewards Earn $50 in Rewards + Free Expedited Delivery – Join Now!
Use eCoupon ORMSAVE10
eCoupon limited to 5 units

ASA5500-CF-256MB= (ASA 5500 SERIES COMPACT FLASH 256MB)
4.6 (5)- N/A
- N/A
- N/A
- N/A
- N/A
- Computer Memory
- DDR4
Est Value$379.37
$15.18
96% offFirst-Time Buyer Discount – Get up to 2% additional off on your first order
ORM Rewards Earn $50 in Rewards + Free Expedited Delivery – Join Now!
Use eCoupon ORMSAVE10
eCoupon limited to 5 units
ASA5505-MEM-512= (512MB MEMORY FOR ASA 5505)
4.6 (5)- 0.3 lbs
- N/A
- Computer Memory
- DDR4
- Desktop / Laptop / Server
- UDIMM
- Dual Channel
Est Value$202.33
$72.84
64% offFirst-Time Buyer Discount – Get up to 2% additional off on your first order
ORM Rewards Earn $50 in Rewards + Free Expedited Delivery – Join Now!
Use eCoupon ORMSAVE10
eCoupon limited to 5 units
ASA5510-MEM-1GB= (1GB MEMORY FOR CISCO ASA 5510)
4.8 (5)- 1.2 inches
- 5.3 inches
- 0.2 lbs
- 0.3 inches
- N/A
- Server
- Computer Memory
Est Value$354.07
$77.90
78% offFirst-Time Buyer Discount – Get up to 2% additional off on your first order
ORM Rewards Earn $50 in Rewards + Free Expedited Delivery – Join Now!
Use eCoupon ORMSAVE10
eCoupon limited to 5 units

ORM Sales Advisors
Buying for your business? Get a personalised quote in under 2 hours. Talk to an expert
LEARNFilters (6)
Questions & Answers
What is the Cisco ASA 5500 series firewall?
The Cisco ASA 5500 series is a family of stateful inspection firewalls that deliver integrated VPN, advanced security services, and flexible deployment for small to medium-size enterprises.
Which models are included in the ASA 5500 series?
The ASA 5500 series comprises six models—ASA 5505, 5510, 5520, 5540, 5550, and 5580—each offering different throughput, interface count, and security module options to suit varied network sizes.
What firewall throughput can the ASA 5500 series deliver?
Throughput ranges from 150 Mbps on the ASA 5505 up to 20 Gbps on the ASA 5580, with actual performance depending on enabled services and hardware module configurations.
Does the ASA 5500 series support VPN connectivity?
Yes. ASA 5500 appliances support both IPsec site-to-site VPN and SSL/DTLS remote-access VPN to secure branch links and mobile users.